
A malicious server attack: ETH Zurich investigation



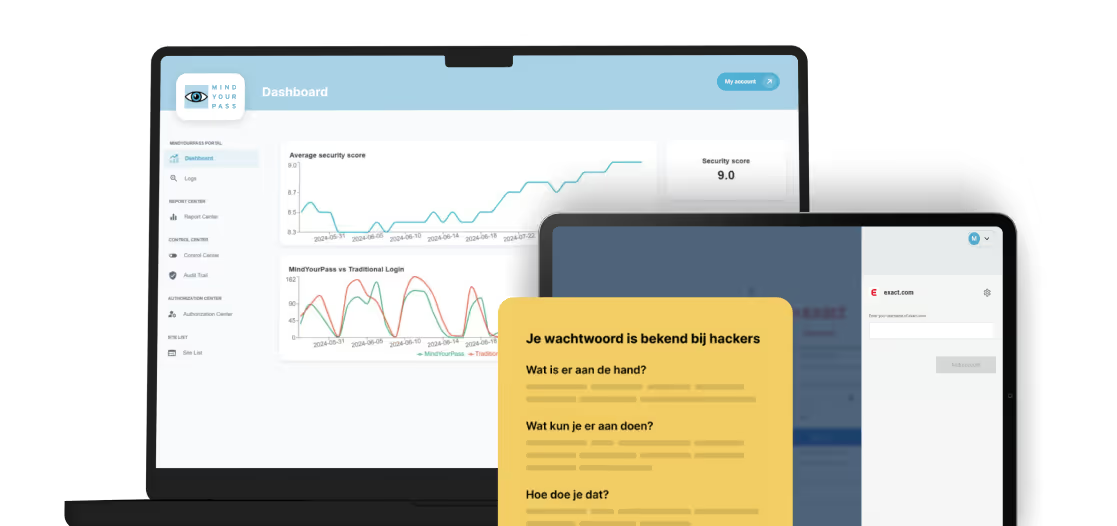



What ETH Zurich's research has shown
In February 2026, researchers from ETH Zurich's Applied Cryptography Group published a peer reviewed paper- accepted at USENIX Security 2026 - showing that three popular password managers Bitwarden, LastPass, and Dashlane) are vulnerable to a fully compromised, malicious server. Under this threat model, an attacker controlling the server can access and even modify passwords stored in user vaults. All three store complete encrypted vaults server-side. Even with strong encryption, a malicious server can manipulate enough of the client interaction to expose or tamper with what a user decrypts — using nothing more than routine actions like logging in or syncing.
How MindYourPass is fundamentally Different
The ETH Zurich attacks work because the servers under investigation contain everything necessary to deduce secrets, except for the decryption step. MindYourPass, on the other hand, was designed from the ground up so that the servers never contain everything. No party - including MindYourPass - has sufficient information to reconstruct user secrets.
- Passwords are never stored. Passwords are not stored anywhere - not on our servers, not in a vault. They are regenerated from a combination of factors each time the user needs them.
- What we store is incomplete by design. We do store factors that make this password regeneration reproducible on all devices. But these factors are deliberately incomplete. By themselves, they are cryptographically worthless - they cannot be used to reconstruct a password.
- The crucial part is only known to the user. The missing element required to complete regeneration only exists in the user's memory. Without it, what we own has no value for anyone - including us.
What we do store - and why that doesn't matter here
We want to be fully transparent about what MindYourPass stores, and why it's completely outside the scope of the ETH findings.
In addition to the regeneration factors, we store the following in an end-to-end encrypted vault, separate from the password regeneration process:
- User names and site information - for convenience, so you don't have to remember it. They play no role in regenerating your passwords.
- PassKey metadata (credential IDs, RPIDs) - enough to locate a passkey, but not the passkey itself. Like passwords, passkeys are generated over and over again and never stored.
- A TOTP input factor - one of several input elements required to regenerate a TOTP seed. The seed itself is never stored.
None of this, individually or combined, is sufficient to reconstruct any of the user's secrets. What we store is always incomplete by design - the missing piece is only known to the user.
Architecture comparison
Our commitment
The ETH Zurich research is a timely reminder that architecture matters - and that "zero-knowledge" is a promise that must be backed by design, not just policy. MindYourPass was built around the principle that no single party, including ourselves, should ever hold enough information to reconstruct a user's secrets. The specific vulnerability class identified by the researchers does not compromise the confidentiality of secrets in MindYourPass.
That said, no system is without its own challenges, and we do not claim to be impenetrable. We see this research as an opportunity to reflect and improve.
Get in touch with us.
Let MindYourPass make your organization safe.

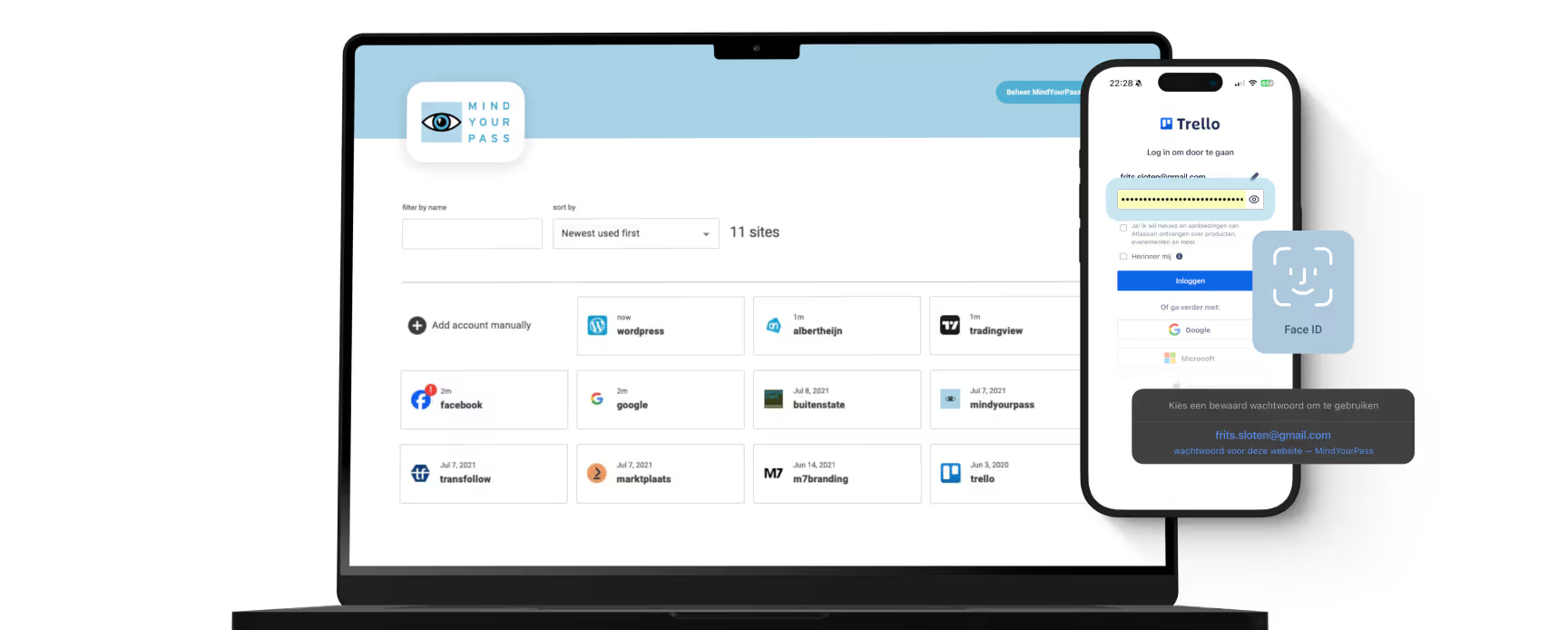
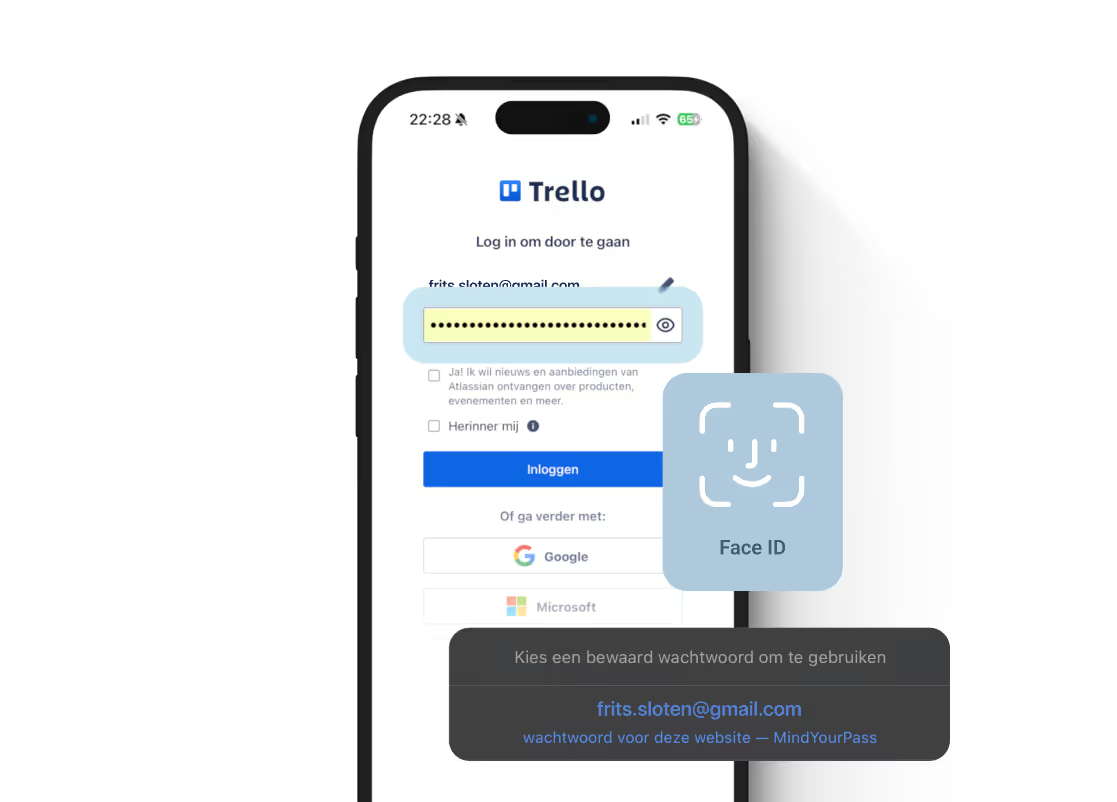
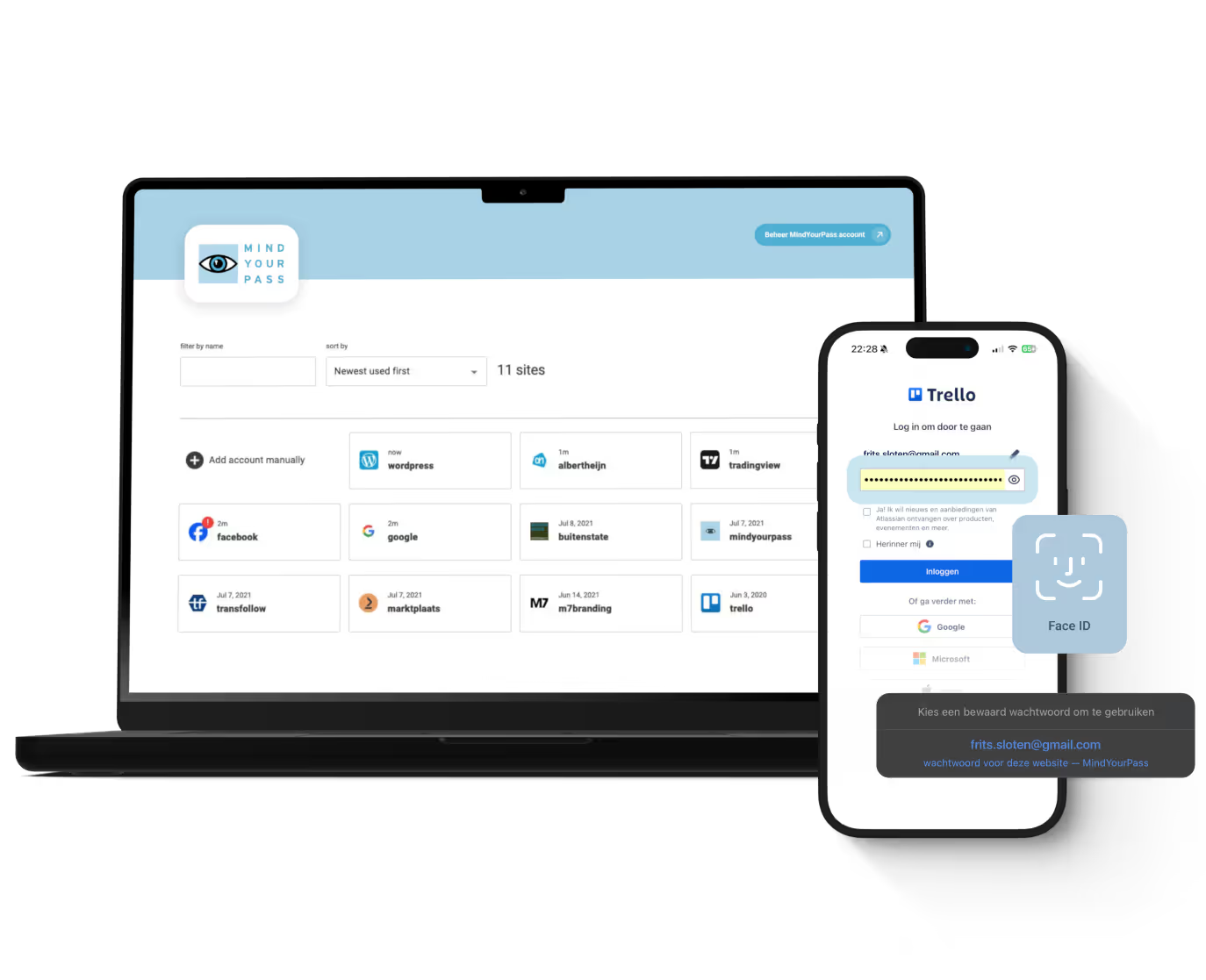
Log in securely with ease.
At home and at work.




Triple-i™ improvement method
De kluisloze wachtwoordmanager van MindYourPass
Met de wachtwoordmanager van MindYourPass maak je eenvoudig al je wachtwoorden ijzersterk en uniek. De wachtwoordmanager beheert jouw wachtwoorden, waarmee jij dagelijks kunt inloggen op al je accounts. Zonder dat jij je wachtwoorden hoeft in te typen. Dat doet MindYourPass voor je.










